Cryptography in general refers to the best possible type of common security procedures which will be including the techniques like confidentiality of data, the integrity of data, authentication and several other kinds of related things. The very basic objective of this particular system is to hide the important information from the hackers and attackers in this particular case so that everybody will be able to get rid of the malicious intent very successfully and there will be no chance of any kind of dangerous element to the organisations. The very basic idea of white box cryptography was generated in the year 2002 and is very much capable of achieving the highest possible level of security without any kind of dedicated hardware in the whole process.
White-box cryptography is the most powerful solution which is capable of protecting the secret keys from being disclosed in the implementation of the software and ultimately this particular aspect will be very much capable of providing people with the safeguarding of the software implementation in the whole process so that overall goals are very easily achieved. Improper competition to this particular system encryption and other methods will be perfectly used within the application coding element so that everything will be carried out very successfully and there will be no chance of any kind of hassle. The very basic motive of this particular system is to bring together the keys in a very unique way so that everyone will be on the right track in dealing with things and they will be no chance of any kind of chaos. This particular cryptography system will be especially critical in terms of developing the systems and will further help in minimising the security race for different kinds of devices very successfully. Hence, the confidential information in this particular case will never be accessible to the concerned people and this particular aspect has been specifically designed with the motive of preventing the exposure to the keys in terms of random systems of data as well as the coding element.
KERCKHOFFS principle of cryptography: In this particular world it is very much important for people to be clear about the designing principles in the world of cryptography in this particular principle very well justify is that the cryptosystem will be required to be completely secure even if other aspects of the system except for the key are available for the public knowledge. The very basic concept of this particular system will be to make sure that principles will be taken into consideration very successfully and everybody will be able to enjoy the openness of the platform throughout the process. This is very well justified that people will be able to have accessibility to different algorithms, implementation, memory and protection techniques so that security will be dealt with very easily and confidential data, as well as secret systems, will be paid proper attention throughout the process.
What is the working of white cryptography?
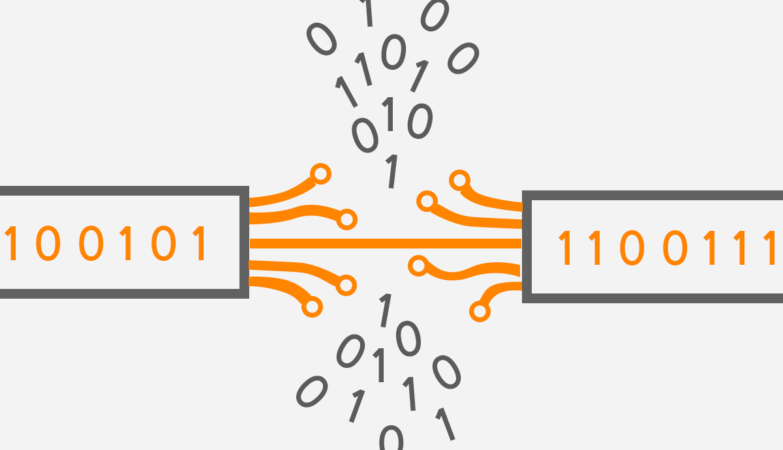
The white box cryptography will be working with the help of several kinds of mathematical techniques to seamlessly blend keys so that application code and secure sensitive cryptographic operations will be paid proper attention without any kind of doubt. This particular aspect will be very much capable of ensuring that keys will be paid proper attention and expression of the hacker’s system will be carried out very successfully so that overall goals are very easily achieved. It is very much vital for the organisations to note down that implementation will be working very uniquely and most of the cases will be very much confidential to be created. Hence, different kinds of white-box implementation will include the different cases of techniques like run time code modification, protection against the static analysis and several other kinds of related aspects. The simple reason behind the popularity of this particular system is that it will be capable of making sure that everything will be carried out successfully including the executable binary system, execution memory and other aspects of the whole process. Some of the very basic steps to be taken into consideration over here to successfully implement the things have been significantly explained as follows:
- Partial evaluation: At the time of operating the things it is very much important for the organisations to make different alterations depending upon the keys for example substitution of the look of the table and several other kinds of related things.
- Tabularizing: Being very much clear about the implementation of this particular aspect is very much important for the different kinds of operations are perfectly transformed in terms of dealing with the transformation of the lookup tables. This will be the best possible way of ensuring that lookup tables will be very much capable of describing any kind of function in the whole process.
- Randomisation: Randomization of this particular system will be very much capable of creating the same functionality in the best possible manner so that overall goals are easily achieved and the algorithm will be paid proper attention without any kind of chaos.
On the overall basis, this particular system is very much capable of making sure that the execution flow and internal data of the algorithm will be paid proper attention and they will be no chance of any kind of difficult scenario in the whole process. The chances of all these kinds of keys being found or expected from the application will be the bare minimum in the whole system and everybody will be on the right track to dealing with the preventive measures without any kind of chaos. Hence, it is very much clear that white box cryptography from the house of companies like AppSealing is the best possible way of ensuring that everything will be carried out very successfully and there will be no chance of any kind of chaos. In this case, the sensitive information of the organisations will be perfectly prevented and data in transit will be paid proper attention without any kind of hassle.